AWS CDK - Infrastructure as Code
Production-Style CI/CD Platform Engineering using AWS CDK (Python)
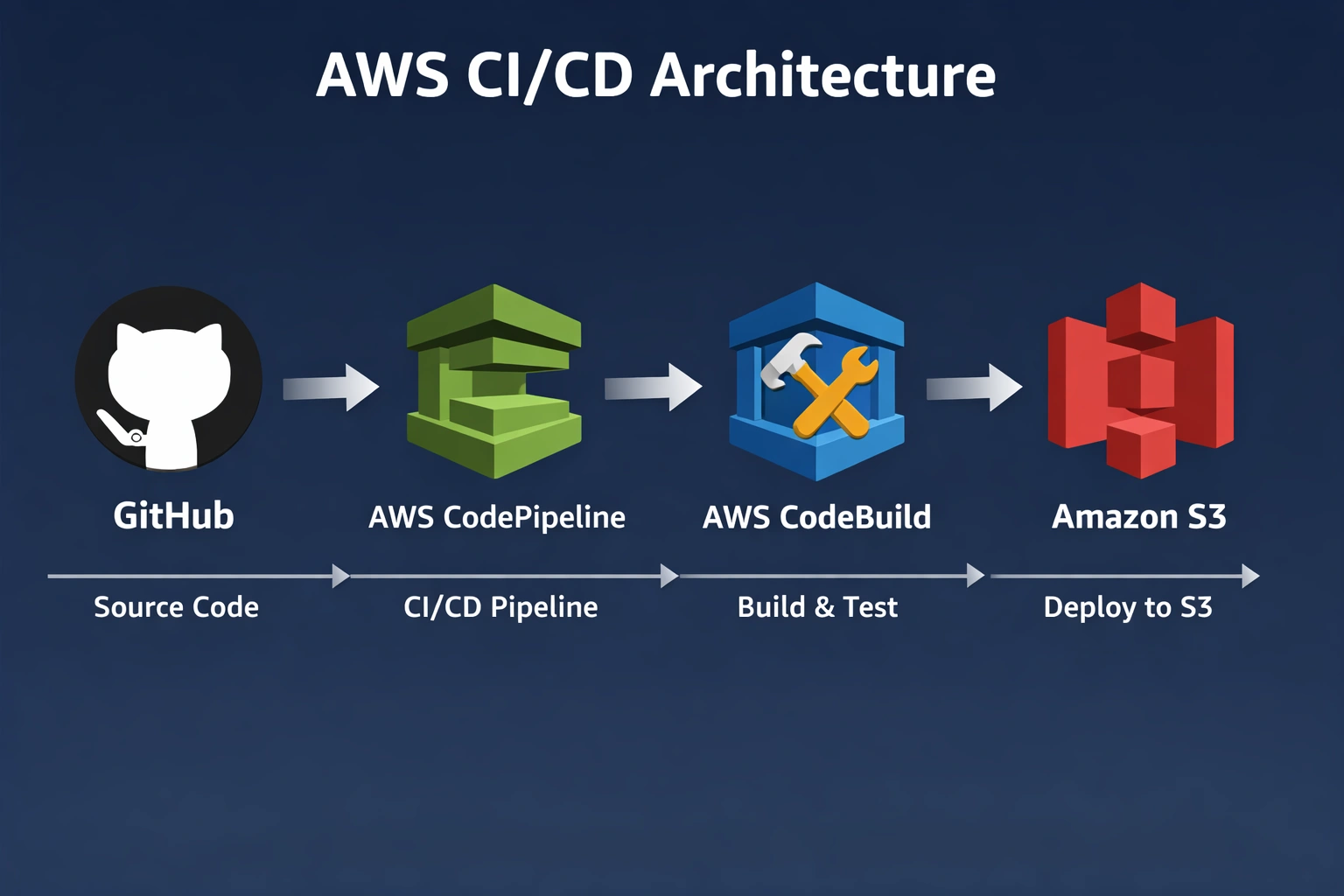
Provisioned a production-style CI/CD platform on AWS using CDK (Python), integrating GitHub source, CodePipeline, CodeBuild, and S3 via Infrastructure as Code. The project eliminated manual, console-based CI/CD setup by making the entire AWS CI/CD pipeline reproducible, version-controlled, and deployable via IaC.
Project Summary
Comprehensive Project Overview
Project Category
DevOps / Platform Engineering (CI/CD Infrastructure)
Industry/Domain
Cloud Infrastructure / DevOps Platforms
DevOps Focus
CI/CD Platform Engineering (Infrastructure as Code)
Key Technologies & Concepts
Core AWS Services Used
AWS CI/CD Keywords
Problem & Objective
What problem did this project solve?
Problems Solved
- Eliminated manual, console-based CI/CD setup by making the entire AWS CI/CD pipeline reproducible, version-controlled, and deployable via Infrastructure as Code
- Reduced setup errors and made the CI/CD platform easy to recreate or modify consistently
- Overcame challenges with secure GitHub integration, IAM permissions, CDK lifecycle management, and pipeline debugging
Primary Objectives
- Provision a reusable CI/CD platform on AWS using Infrastructure as Code (AWS CDK in Python)
- Automatically integrate GitHub source with CodePipeline and CodeBuild for consistent, repeatable build automation
- Implement environment separation logically via pipeline stages and deployment targets (S3 stage/prod paths)
Solution & Architecture
Architectural Overview
Solution Overview
Designed and deployed a CI/CD platform on AWS using AWS CDK (Python) to provision CodePipeline (orchestration), CodeBuild (build automation), IAM roles, Secrets Manager (GitHub token), and S3 (artifacts), enabling reproducible, version-controlled pipeline infrastructure sourced from GitHub.
Environment separation is implemented logically via pipeline stages and deployment targets (S3 stage/prod paths), mirroring environment constructs used in Azure and GCP.
The solution uses managed AWS CI/CD services (CodePipeline and CodeBuild) providing built-in availability and fault tolerance, with stateless builds improving reliability and reducing drift.
Key Components
- AWS CDK (Python) - Infrastructure as Code framework
- AWS CloudFormation - IaC backend (via CDK synth)
- AWS CodePipeline - CI/CD orchestration service
- AWS CodeBuild - Build automation service
- GitHub - Source repository
- AWS Secrets Manager - GitHub token management
- Amazon S3 - Build artifact storage
- IAM Roles & Policies - Pipeline security
- Buildspec.yaml - Build instructions (written directly in the IaC)
Skills & Technologies Used
Technical Proficiency Demonstrated
Primary Skills
- AWS CDK (Python) - Intermediate
- CI/CD Platform Engineering - Intermediate
- AWS CodePipeline - Intermediate
- AWS CodeBuild - Intermediate
- Infrastructure as Code (IaC) - Intermediate
- AWS IAM (Roles & Policies) - Intermediate
Secondary Tools / Frameworks
- AWS CloudFormation (via CDK synth)
- AWS Secrets Manager
- Amazon S3
- GitHub
- Buildspec.yaml
- AWS CLI
Programming Languages
- Python - Primary language for AWS CDK IaC development
- YAML - For CloudFormation templates and build specifications
- JSON - Configuration and output formats
AWS Cloud & DevOps Tools
Pipeline Implementation & Challenges
Technical implementation details and problem-solving
Pipeline Flow
- CDK (Cloud Deployment Kit) transforms Python script into CloudFormation template via
cdk synth - Two-stage CI/CD Pipeline: Source (GitHub) → Build (CodeBuild)
- Source code fetched from GitHub using OAuth token stored in AWS Secrets Manager
- Build executed in Linux environment (Ubuntu) using buildspec.yaml instructions
- Artifacts stored in Amazon S3 bucket for deployment
Key Technical Challenges
- Configuring secure GitHub integration using OAuth tokens stored in AWS Secrets Manager
- Setting up correct IAM roles and permissions for CodePipeline and CodeBuild to access S3, Secrets Manager, and source actions
- Understanding and managing the CDK lifecycle (bootstrap, synth, deploy) and CloudFormation stack dependencies
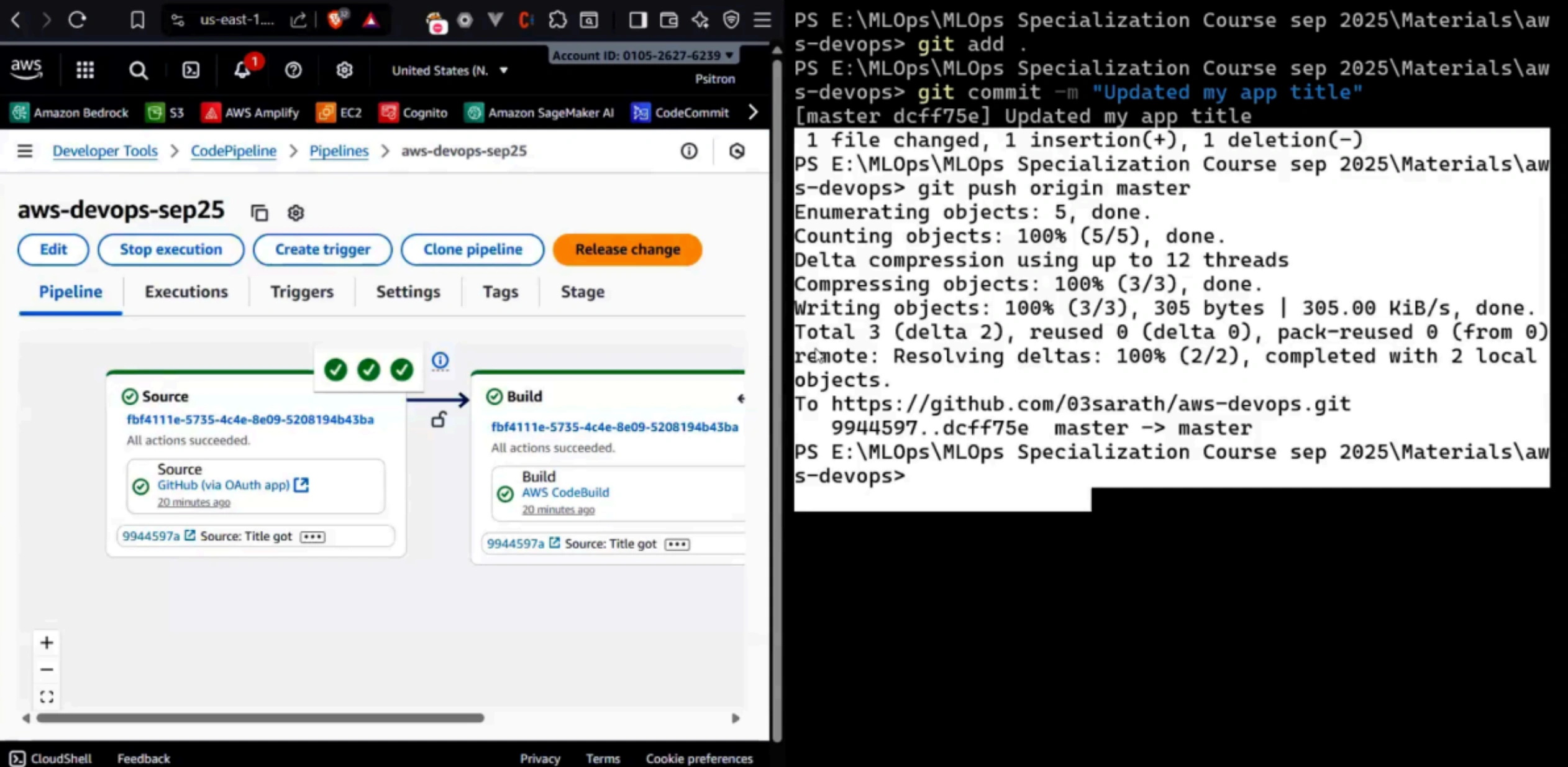
- Debugging pipeline execution failures using CodeBuild logs and CodePipeline stage outputs
How They Were Resolved
- GitHub integration: Generated a GitHub token and securely stored it in AWS Secrets Manager, then referenced it in the CDK stack
- IAM permissions: Defined and adjusted IAM roles/policies for CodePipeline and CodeBuild to grant least-privilege access to required services
- CDK lifecycle issues: Used
cdk bootstrap → cdk synth → cdk deployto correctly provision prerequisites - Pipeline failures: Inspected CodeBuild logs and CodePipeline stage outputs to identify misconfigurations and iteratively fixed them
AWS DevOps CI/CD - Architecture & YAML Mapping
Architecture to AWS construct mapping
| Architecture Block | AWS CI/CD Construct |
|---|---|
| CodeCommit / GitHub | Source action (CodePipeline) / GitHub webhook |
| AWS CodePipeline | Pipeline root, Stages |
| Linux Runner | CodeBuild environment (environment: type: LINUX_CONTAINER) |
| Build Stage | CodeBuild project (buildspec.yml → phases) |
| Artifact Storage | Amazon S3 / Amazon ECR |
| Deployment Target | AWS CodeDeploy / ECS / EC2 / S3 |
| Security & Auth | IAM roles & policies |
| Logs & Monitoring | CloudWatch Logs |
Pipeline Execution Evidence
Proof of successful implementation
Git Integration Evidence
GitHub repository showing code changes and commit history triggering the CI/CD pipeline.
Assets & References
Code, diagrams, study material
GitHub Repository
Source code repository containing AWS CDK Python implementation for CI/CD pipeline.
Access Repository